Drift Protocol, a decentralized cryptocurrency exchange (DEX), says the recent exploit against the platform was a six-month-long, highly coordinated attack.
In an X post on Saturday, Drift said ‘The preliminary investigation shows that D drift was part of a structured intelligence operation with organizational support, significant resources and months of deliberate preparation.
The decentralized exchange was exploited on Wednesday, with external estimates putting losses at around $280 million.
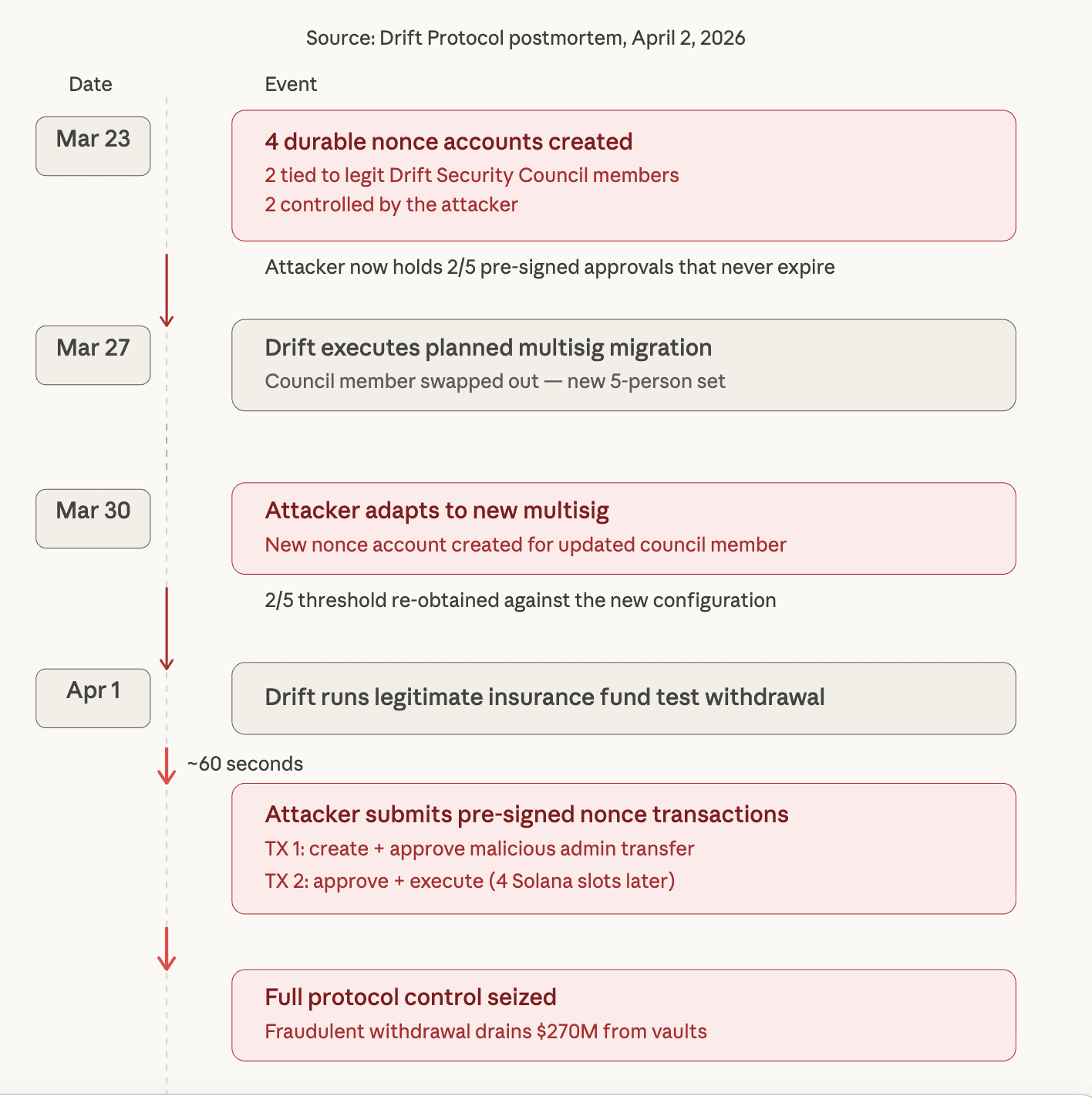
It all began at a “major crypto conference”
Drift says the attack plan dates back to around October 2025, when “savage actors posing as a quantitative trading firm” first approached D drift contributors at’major crypto conference,” saying they would like to integrate with the protocol.

Source: Drift Protocol
Source: Drift Protocol
Over the next six months, the group continued to engage in person with contributors at several industry events. But this seems to be a targeted approach, where people from this group continued to deliberately seek out and engage certain Drift contributors,” said Diffr.
“They were technically fluent, had verifiable professional backgrounds, and were familiar with how Drift operated,” Drift said.
Having established trust and access to Drift Protocol over six months they used shared malicious links and tools to compromise contributors’ devices, execute the exploit (and then erased their presence immediately after the attack).
The incident also serves as an example of how crypto industry participants must remain cautious, even during in-person interactions, to be alerted and skeptical; for instance, the emergence of crypto conferences can serve as prime targets for sophisticated threat actors.
Drift flags a high probability of a Radiant Capital hack link
The exploit was executed by the actors behind the October 2024 Radiant Capital hack, Drift said with’medium-high confidence’ that it was carried out by “the same actors who did this,” D drift said.
According to Radiant Capital in December 2024, “the exploit was executed using malware sent via Telegram from a North Korea-aligned hacker who is seen as an ex-contractor.”
Source: Dith
Source: Dith
Originally shared for feedback by other developers, this ZIP file was ultimately malware that helped to fuel the subsequent intrusion, Radiant Capital said.
Drift said it is “important to note” that the individuals who appeared in person “were not North Korean nationals.”
Related: Naoris launches post-quantum blockchain as quantum security risks gain attention
“DPRK threat actors operating at this level are known to deploy third-party intermediaries to conduct face-to-face relationship-building,” Drift said.
Drift said it is working with police and others in the crypto industry to “build a full picture of what happened during April 1st attack,” Diff said. Paraphrast.
Magazine: Bitcoin 85% crashes ‘done,’ CLARITY Act speculation mounts: Hodler’s Digest, Mar. 29 – April 4
Thanks for reading Drift Protocol $280M exploit took months of deliberate preparation