The attack on Drift Protocol was not a hack in the traditional sense.
Nobody found a bug or cracked a private key. There wasn’t a flash loan exploit or manipulated oracle either.
Instead, an attacker smuggled Drift’s security council with a legitimate Solana feature called ‘durable nonces’ to trick weeks later pre-approving transactions that would be carried out at arbitrary time and in. context the signers never intended for them on their behalf.
It led to an at least $270 million drain of less than a minute to execute but more than one week to set up.
What durable nonces are and why they exist
All transactions are accompanied by a’recent blockhash,’ on Solana — it is essentially stamp that proves the transaction was made recently. About 60 to 90 seconds later, that blockhash expires after about 60 or 90 Sekunden for . This transactions are not submitted to the network within that window, and if it is not accepted by the transaction (i.e. It’s a safety feature that helps prevent old, stale transactions from being replayed later on.
Safety Durable nonces override that feature of . A fixed ‘nonce,’ is one-time code stored in a special onchain account (the expiring blockhash) that replaces the expiry block Hash with an original “non” which keeps the transaction valid for life until someone decides to submit it.
That feature can be used for legitimate reasons, and is also a valid one. It is essential for hardware wallets, offline signing setups and institutional custody solutions that can prepare and approve transactions without being required to submit them within 90 seconds.
A problem is that indefinitely valid transactions are a problem, but this does not mean the same thing as s. The system’s hardcoded rules allow for the execution of a transaction that can be executed next week or next month if one can get someone to sign it today. After approval is granted, the signer has no option to revoke his or her permission except for manually advanced nonce account (most users do not monitor their nonCE account).
How the attacker used them
In Drift’s protocol, the ‘Security Council multisig,’ system was in which more than one person (in this case five) share control and any action requires at least two of them to approve. DeFi is a standard security practice, where the concept of multisigs (compromising one single person) is not enough to steal money.
But it was no need for the attacker to ‘break down anyone’s keys’ that someone had been key. All they needed were two signatures, and appear to have been obtained through what Drift calls “unauthorized or misrepresented transaction approvals,” meaning that the signers likely believed they were approving a routine transaction.
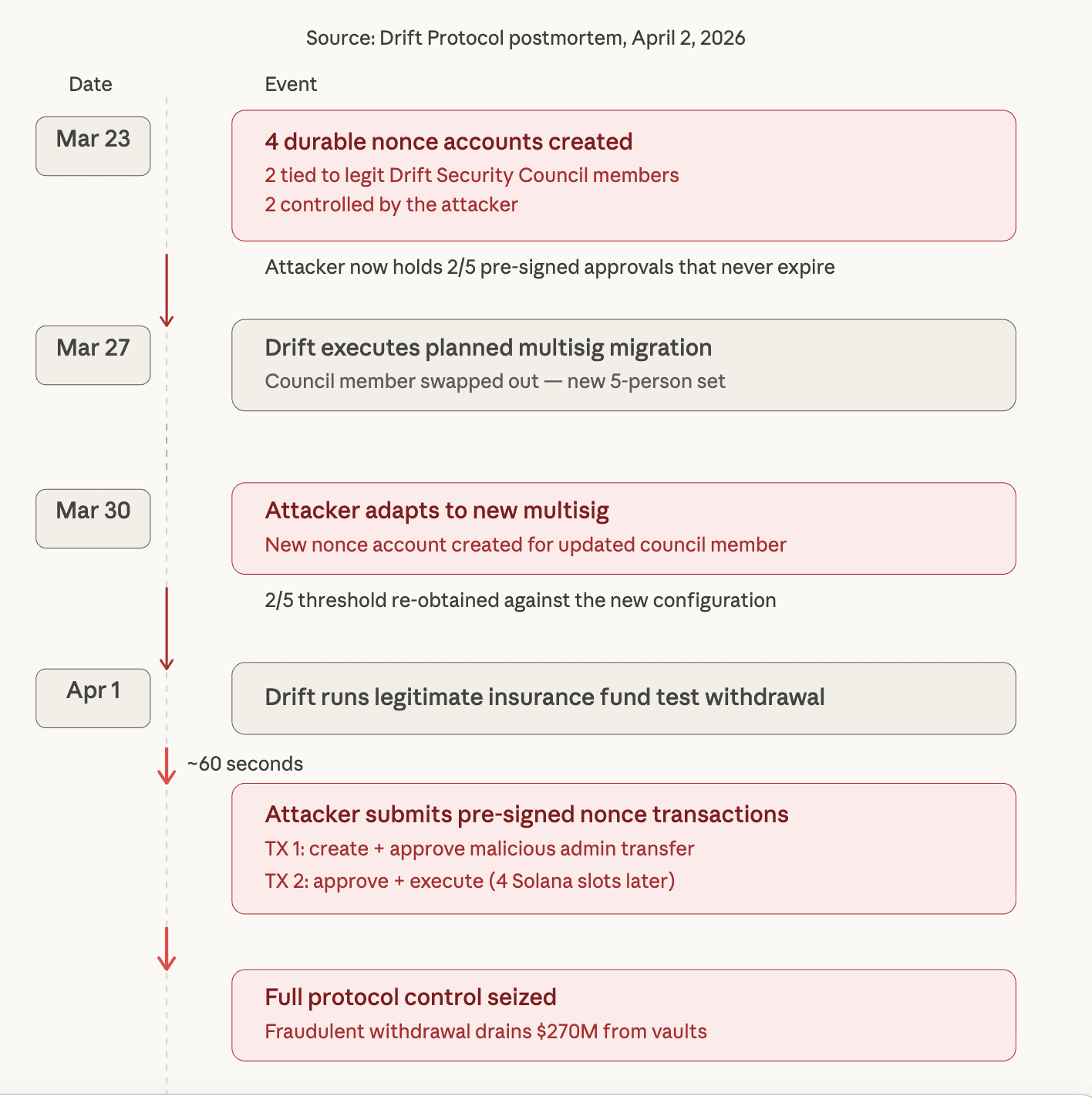
Here is the timeline Drift published in a Thursday X post.
Four long nonce accounts were made on March 23. The two were related with legitimate members of the Drift Security Council. The attacker dominated two s. That is, as such, the attacker had already obtained valid signatures from two of the five council members who were locked into long-lasting nonce transactions that would not expire.
Drift arranged an attempted Security Council migration to replace a council member on March 27. A adapted for the attacker. The new long-lasting nonce account, linked to a member of the updated multisig, appeared by March 30, meaning that the attacker had reached the two approval threshold required under the new configuration.
On April 1, the attacker executed.
Initially, Drift had a legitimate test withdrawal from its insurance policy. An attacker submitted the pre-signed durable nonce transactions about a minute later, when they signed them. The two transactions, four slots apart on the Solana blockchain, were enough to create and approve a malicious admin transfer (and then approve and execute it).
Within minutes the attacker was in full control of Drift’s protocol-level permissions. That control was used by them to introduce a fraud withdrawal mechanism and drain vaults.
What was taken and where it went
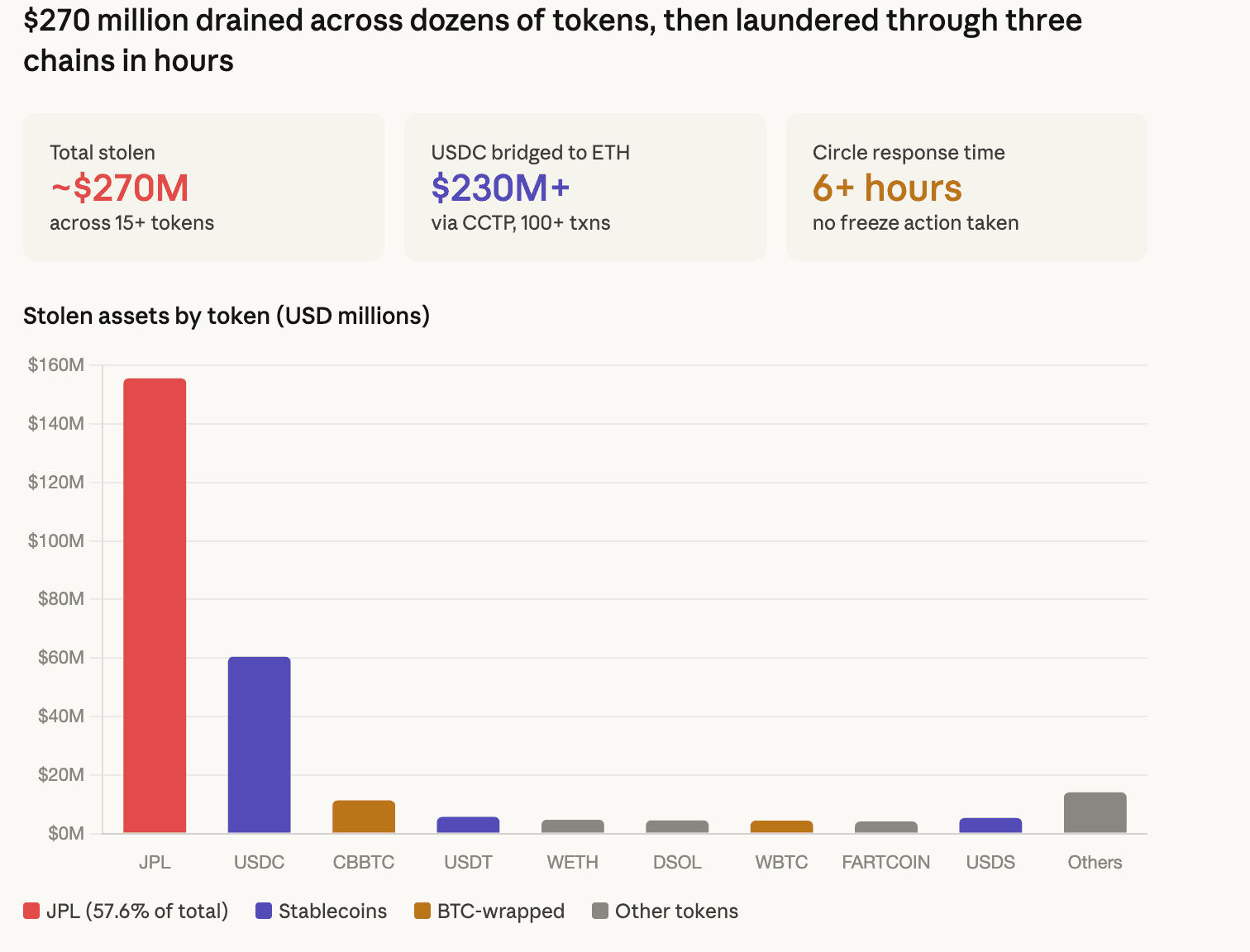
Fund flows were analyzed by onchain researchers in real time, and tracked by the fund flows. Security research researcher Vladimir S The collapse of seized property,compiled by Vladimir A.Stylosa? The total was about $270 million, or roughly $270,000 million in dozens of tokens for a .
The biggest category was $1555, the largest single category. JPL tokens 6 million in JP, $60 million after . $11 million in $USDC, 4 million for paraphrasing. CBBTC 3 million (Coinbase wrapped bitcoin), $5 million, a of $3million. In USDT, $4 – 65 million in $M, $6 million. In wrapped ether, $4 million (7m) is $7 million in wrapped-ether. In DSOL, $4, 5 million in . 4 million in WBTC, $4 million for . A million in FARTCOIN and smaller numbers across JUP, the Japanese National Institute of Health and Security (JITOSOL), MSOL, BSOL; EURC or other.
Efforts were made to fund the primary drainer wallet eight days before the attack via NEAR Protocol intents but did not appear until execution day. A few days later, the money was transferred to intermediary wallets that were funded just the day before by Backpack, a decentralized crypto exchange which requires identity verification, possibly giving investigator an indication of what might be their lead.
There, money was transferred to Ethereum addresses via Wormhole, a cross-chain bridge from there. Torado cash — a sanctioned privacy mixer, had been used to fund those Ethereum addresses before it was delivered through Tornado Cash.
The most important onchain investigator, ZachXBT (a prominent spokesman for the investigation) noted that more than $230 million in $USDC was transferred from Solana to Ethereum through Circle’s CCTP (Cross-Chain Transfer Protocol) over over 100 transactions.
His criticism of Circle, the centralized issuer of $USDC, for not freezing the stolen money during a six-hour window after the attack began around noon Eastern time.
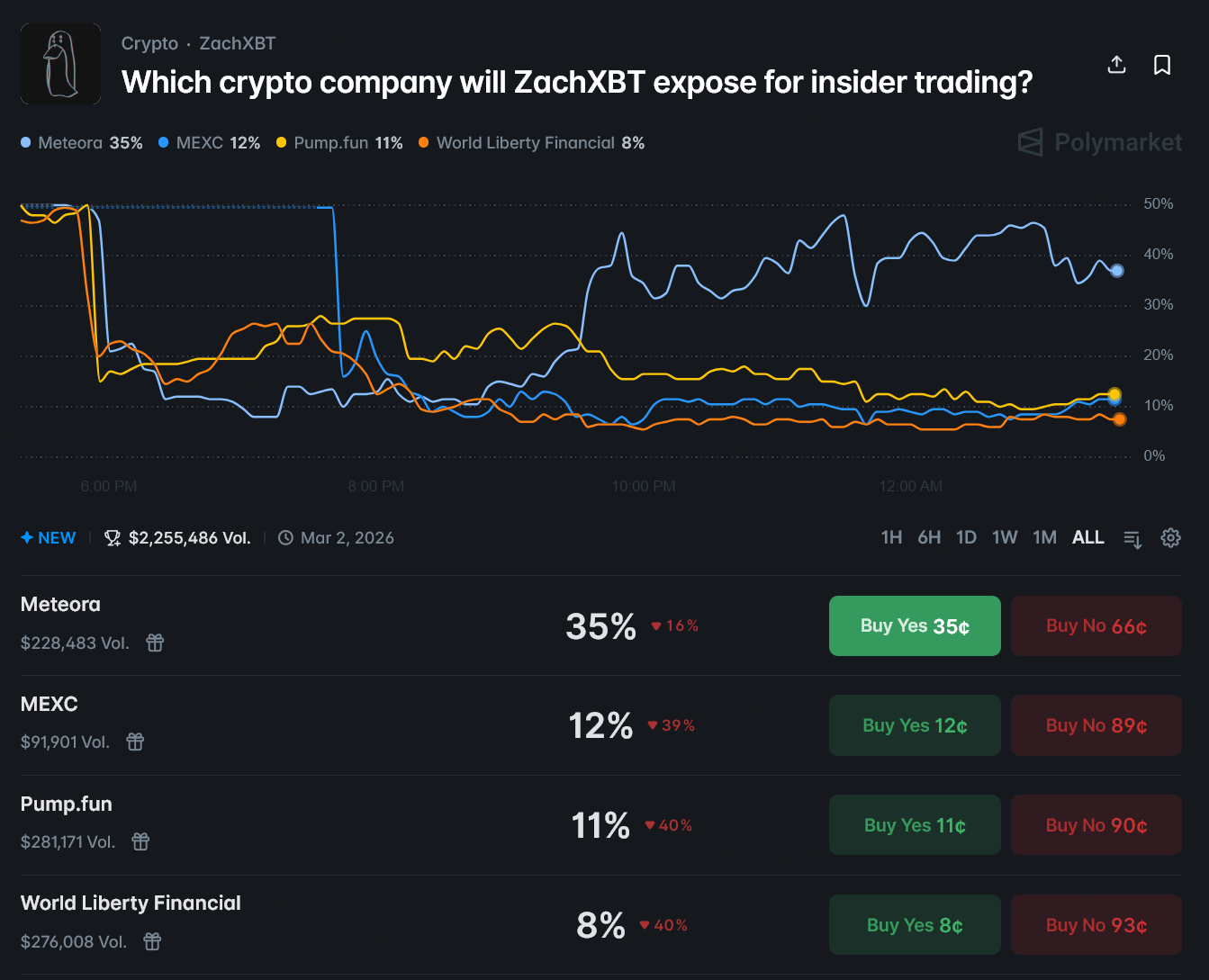
A user whose Twitter feeds the phrase ‘Temmy’ tweet was also similar to those of recent social engineering efforts that were used in an attack, which has been seen before and is now using tactics like they have done. It’s been a who has said ‘We’ve seen this before. The user said ‘We have seen this so many times.
bit of a , “by bit” a $1, and the. A 4 billion is. Infringing the signing infrastructure, the attacker swayed signers into authorizing malicious transactions and trickeD signed signs to write malware. the same idea as . social engineering . not a coder, but . The ronin bridge is for . $625 million. Validator keys were hacked and the validator key was stolen. same story, . a cetus protocol, which s. $223 million for ,. different way but same result. Has anyone done hundreds of millions for paraphrasing? post said ‘It was paraphrasing the comment.
What was not compromised
What was the failure of the human layer around the multisig? The attacker was able to separate the moment of approval from the time of execution by over a week, which created ‘the context of the signed document no longer corresponded with the context in which it was used.
All deposits into Drift’s borrow-and-lend products, vault deposits and trading funds are affected by all deposits to the product. DSOL tokens notdeposited in Drift, such assets held to the D drift validator, are unaffected. paraphrasing insurance fund assets are being pulled out and protected from. Protocol is frozen, and the wallet has been removed from the multisig after being hacked.
As such, this is the third major hack in recent months that did not involve a code vulnerability. DeFi protocols are increasingly being left by money, rather than smart contract bugs, and social engineering and operational security failures (i.e.
Its long nonce vector is particularly dangerous because it exploits a feature that exists for good reason and can’t be easily justified against without fundamentally changing how multisig approvals work on Solana.
The open question, which Drift’s upcoming detailed postmortem will have to answer, is how two separate multisig members approved transactions they did not understand and whether any tooling or interface changes could have marked durable nonce transactions as needing further scrutiny.
Read more: North Koreans hackers likely behind $286 million Drift Protocol exploit
Thanks for reading How a Solana feature designed for convenience let attackers drain more than $270 million from Drift