A digital shadow war is escalating, and this time, Google’s own technology is being weaponized. North Korea’s notorious Konni hackers have unleashed a chilling new attack, exploiting the ‘Find My Device’ network – a feature designed to protect users, now turned against them. This marks a disturbing first: Konni is leveraging Google’s Find My network to target both Android and Windows systems, turning your lost-and-found lifeline into a data-stealing, remote-control gateway. Are you safe?
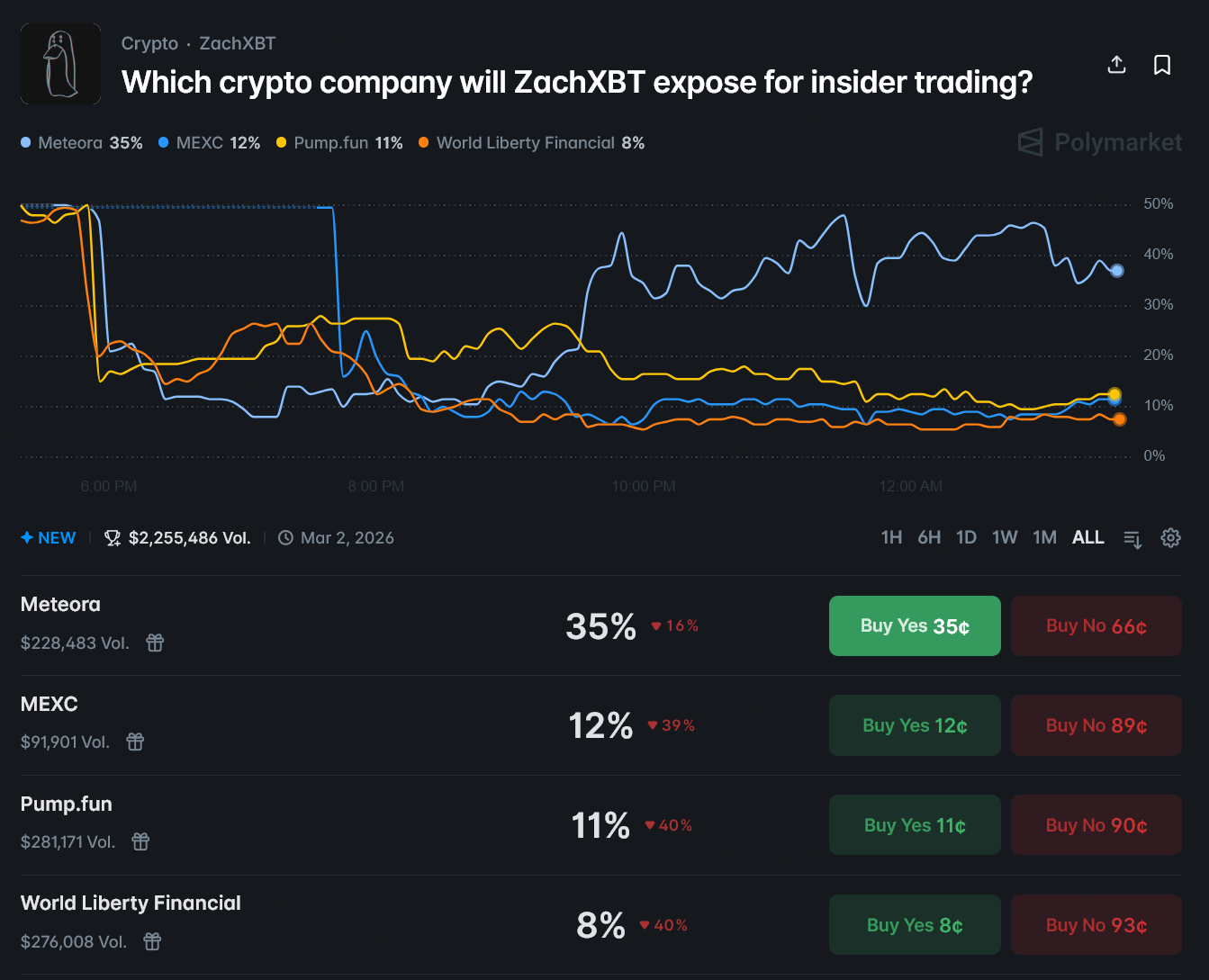
Early September 2025: a digital shadow war escalated. Hackers discovered a chilling exploit within Google’s Find Hub, turning asset tracking into a weapon capable of remotely wiping personal data.
Imagine this: a digital serpent named Konni slithers into your inbox, disguised as a harmless email. This is the first strike in a meticulously crafted attack chain, a spear-phishing campaign designed to unlock the gates to your digital kingdom. Once inside, Konni doesn’t stop there. It exploits your trust, hijacking active KakaoTalk sessions to spread poisoned ZIP archives to your unsuspecting contacts. It’s a digital betrayal, turning your trusted messenger against you.
Cybercriminals are stooping to new lows, exploiting vulnerable individuals under immense stress. According to a chilling report from the Genians Security Centre (GSC), attackers are masquerading as compassionate figures psychological counselors and North Korean human rights advocates luring victims with seemingly helpful “stress-relief programs” that are actually cleverly disguised malware.
South Korean cybersecurity group says malware is for Korea-focused operations
Spear-phishing attacks are getting dangerously clever, masquerading as official communications from trusted sources like the National Tax Service. One wrong click, and you’re not just opening an email, you’re unlocking your entire computer for hackers. These malicious emails carry booby-trapped attachments unleashing Remote Access Trojans (RATs) like Lilith RAT, which gives cybercriminals complete control, turning your machine into a puppet to spread further infections.
Imagine your webcam, silently watching, even when you’re not there. Hackers aren’t just breaking in; they’re setting up shop, turning your computer into a long-term surveillance hub. We’re talking over a year of undetected access, a digital squatter pulling strings from the shadows. As GSC warns, the initial breach is just the beginning. It’s a gateway to total system control, a data-vacuum, all cloaked in sophisticated evasion tech designed to keep them invisible. Think of it as a digital ghost, haunting your system, unseen and unheard, for far too long.
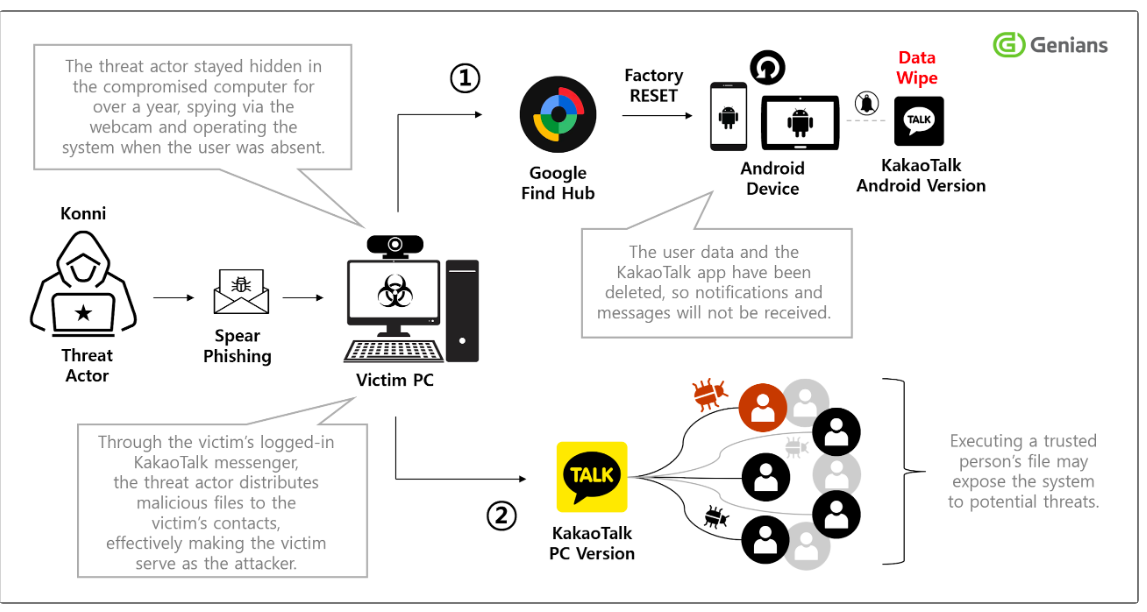
Konni attack flow. Source: The Hacker News
Google and Naver accounts are prime targets for hackers. Once they crack your Google password, it’s game over: they can remotely wipe your devices using Google’s Find My Device feature, leaving you digitally stranded.
Imagine a digital thief, slipping into Naver’s email fortress. Their first act? Erasing Google’s security alarms – the digital equivalent of silencing the smoke detector. But they didn’t stop there; the digital trash can was emptied, a desperate attempt to bury the evidence of their intrusion.
Imagine receiving a seemingly harmless ZIP file through a messaging app. Unzip it, and you unleash a digital wolf in sheep’s clothing: “Stress Clear.msi,” a malicious Microsoft Installer package. The trick? It’s sporting a legitimate signature, courtesy of a Chinese company, making it appear trustworthy. But once executed, this Trojan horse drops the facade, unleashing a stealthy batch script to prepare your system for infiltration.
The malware then unleashes a cleverly disguised Visual Basic Script, flashing a bogus “Language Pack Incompatibility” error on the screen. Unbeknownst to the user, this distraction is a smoke and mirrors act, concealing the execution of malicious commands silently wreaking havoc in the shadows.
While echoes of the Lilith RAT reverberate through its code, a new threat emerges: EndRAT (dubbed EndClient RAT by security researcher Ovi Liber). This isn’t just a rehash; EndRAT bears the mark of significant evolution, a chilling testament to the ever-shifting landscape of cyber threats.
Konni APT, notorious for its stealth, is escalating its attacks, starting with an AutoIt script to deploy Remcos RAT v7.0.4 a Trojan unveiled by its own maintainers on September 10, 2025. But that’s old news. The threat actors have upgraded their arsenal, wielding newer, more potent Remcos variants. Adding to the chaos, security researchers discovered traces of Quasar RAT and RftRAT a favorite of the Kimsuky group back in 2023 lurk on compromised systems, suggesting a complex, multi-layered attack strategy.
A South Korean cybersecurity firm believes it has unearthed digital espionage tailored specifically to the peninsula. Deciphering the malware’s code and its targets, however, requires a deep dive and considerable resources, hinting at a sophisticated, Korea-centric operation.
North Korea-backed hackers’ impetus grows
This strike bears the unmistakable fingerprints of the Konni APT campaign – a digital assault orchestrated from the shadows and linked to North Korea’s notorious Kimsuky and APT 37 hacking collectives.
Lazarus Group is back, and this time they’re packing an upgraded Comebacker malware. ENKI exposed their latest espionage campaign, targeting defense and aerospace giants. Their weapon of choice? Deceptive Microsoft Word documents, meticulously crafted to appear as legitimate communications from industry titans like Airbus, the Edge Group, and even the prestigious Indian Institute of Technology Kanpur. Don’t fall for the bait.
Pyongyang’s digital delinquencies may soon trigger Seoul’s wrath. Cryptopolitan reports South Korea’s Second Vice Foreign Minister Kim Ji-na revealed the nation is weighing sanctions against North Korea in response to escalating cryptocurrency-related crime. The key, she emphasized, is a united front with the United States.
Thanks for reading North Korea-backed group hijacks Google’s Find Hub in credential theft campaign